“Hi there, I’m hoping you can help me out.”It’s the beginning of a standard customer service call. One of your customers has an issue or slight inconvenience they are trying to solve. Fortunately, the person on the other end of the line is a people pleaser, trained to assist as conveniently as possible. More often than not, these calls have a happy ending.
However, this routine call can also be the beginning of a devastating attack. Allow me to explain.
It’s called SIM Swapping (or SIM Hijacking) and you may have heard about it in the news. A leading cryptocurrency investor was robbed of $24 million. Private citizens have had hundreds of thousands of dollars stolen. The attacks are often targeted, can happen in minutes, and can leave your customers devasted.As these attacks grow in frequency, the impacts have expanded. Recently, victims have begun to levy massive lawsuits against their cellular carriers for allowing such fraud to exist. The argument? As one lawsuit put it,”What AT&T did was like a hotel giving a thief with a fake ID a room key and a key to the room safe to steal jewelry in the safe from the rightful owner.”
How these lawsuits shake out remains to be seen, but understanding the attacks and how to stop them is actually quite clear.
Table of Contents
How Does a SIM Swap Attack Work?
The way the attack works is a fraudster first identifies their target and learns as much as they can about them. They gather their phone number and carrier, and any information they may need to trick customer service into believing they are this person, such as addresses, maiden names, etc. They will then call in posing as the customer, “Hi there, I’m hoping you can help me outÉ”
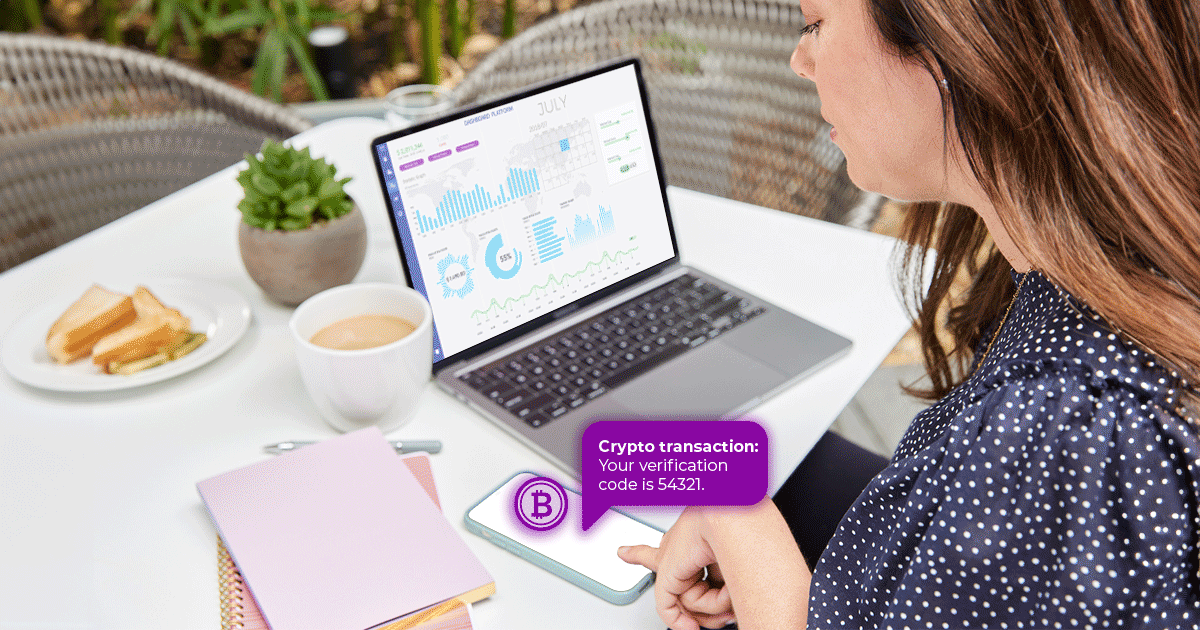
They will likely share a sob story about how they lost their phone and need their number Ôswapped’ to a new SIM card (or ported to a new carrier if their story is that they are “switching carriers”). Depending on the performance of the con man, a sympathetic customer service rep might transfer that number. If this happens, the fraudster now has access to that phone number and every communication sent to it, including one-time passcodes sent to verify account access.
Uh oh.
You can imagine what happens next. A bank account can be drained, a cryptocurrency wallet emptied, or emails and social media accounts hacked. Within a matter of seconds an entire life can be destroyed, and your brand could be included in the blame for it.
But it doesn’t have to be this way.
How Can You Stop SIM Swap Attacks?
The solution is actually quite simple. Knowing when a user activated their current SIM card (or last ported their number) could stop this attack.
By using SIM Activation Timestamp, any business can stop this attack in its tracks. Notably banks, cryptocurrencies, social media, and all forms of e-commerce companies where customers have high-value accounts are most at risk, but really any business can benefit from monitoring exactly when a customer’s SIM card was activated to block such fraud. Not only would you be protecting their customers, you could be shielding yourselves from costly lawsuits that could cause permanent damage to your brand. A quarter billion dollar lawsuit is one thing, but a loss of trust can last forever.
Don’t leave your customers open to unnecessary risk and don’t become the next negative headline. If it can happen to some of the biggest crypto investors in the world, it can certainly happen to you.
Contact Telesign to learn more.