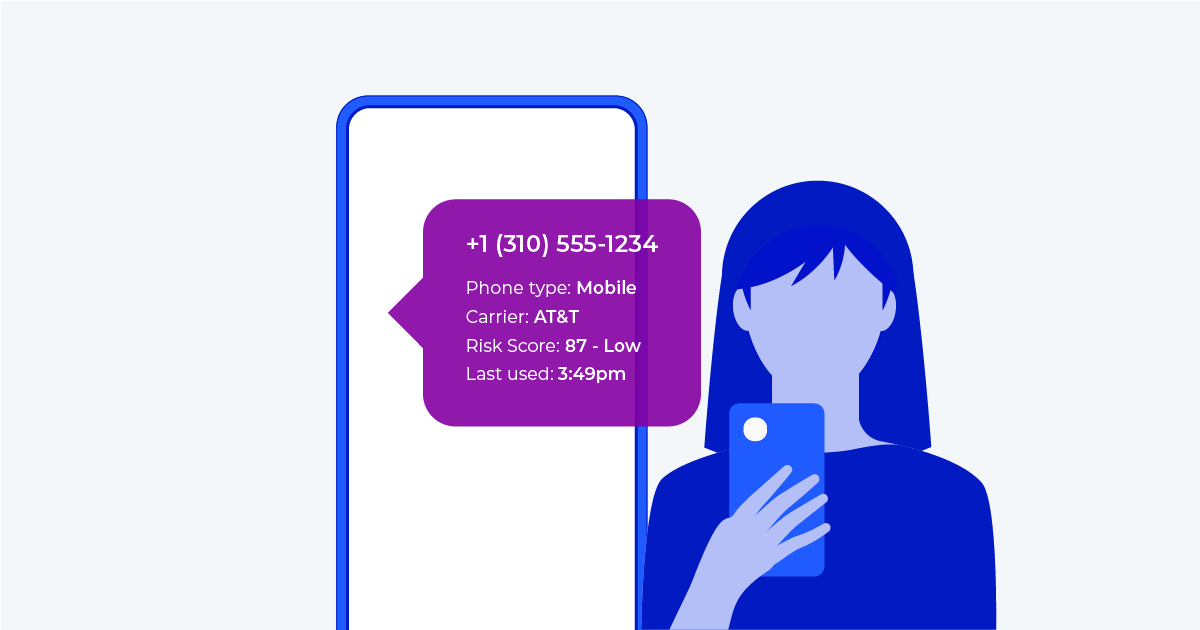
We have mentioned before that the entire linchpin of digital identity relies on the collection of a phone number as a global trust anchor. Today, you will learn how Telesign analyzes phone numbers in fraud prediction models to help you decide whether or not to onboard a user onto your web ecosystem.
First let’s look at the different type of phone numbers. Traditionally, the majority of phone numbers were land lines but as the world has gone increasingly digital, we now think of a phone number as a cell phone. Cell phones are an interesting use case for identity because they are inextricably linked to one person. While some folks may opt to have a separate work phone, the overwhelming majority of users carry one and rarely change the number. (As opposed to something like e-mail where most people use multiple for different purposes)
Pre-paid vs. Post-paid
Beyond looking at just a cell phone and the information you provide to your carrier, there are two important distinctions. Your cell phone is either post-paid or pre-paid. A post-paid cell phone is when a carrier (AT&T, Verizon, etc.) sends a bill every month. This is typically indicative of a good user. By providing real information to a large telecommunications company, Telesign’s risk model assesses that this person is less likely to commit fraud.
A pre-paid phone does not necessarily mean that the user is a fraudster, but Telesign can tell the difference between a pre-paid smart phone that is on the T-Mobile network (think about foreign nationals in the US that do not have a credit score) and a $7 flip phone purchased at a 7-11. Again none of these data points are automatically disqualifying, but you can start to see how Telesign builds out a risk profile based on a phone number.
Voice Over IP
Traditional cell phones aren’t the only way to acquire a phone number though, many providers offer VOIP numbers free of charge or very cheap. There are legitimate reasons to use these virtual numbers, such as affordable long distance calling. However, many fraudsters acquire these numbers to create fraudulent accounts that then cause chaos on your platform. Telesign can detect VOIP numbers and a business could customize their onboarding settings to automatically flag these accounts for manual review.
SIM Card Fraud
What are other things we look for? Information that does not match. A user that claims a location that differs from the registration address on their cell phone is suspicious. Furthermore, we can look at device type, and the origin of a SIM card. A SIM Card registered to Africa and operating in America also raises some concerns. We can look at the porting history of a cell phone. If a number was recently moved to a new phone and is starting to create accounts immediately, Telesign can infer that malintent may exist. This could be a phone that is participating in SIM Swap, one of the most devastating forms of fraud.
In total, Telesign uses APIs to run dozens of checks for onboarding protection. When paired with 2FA, digital identity can provide a holistic solution that can eliminate bad actors from entering your platform. By doing that you protect your users by reducing spam, fake accounts, bulk phishing and can even stop account takeover. You also seamlessly streamline your onboarding process which leads to more real users and more real revenue.
Telesign has been connecting and protecting online experiences for over 15 years. We support 21 of the 25 largest web properties in the world and we’re prepared to help you. Contact Telesign now and learn more about how to keep your platform safe.